Every Sensitive Record.
At your fingertips.
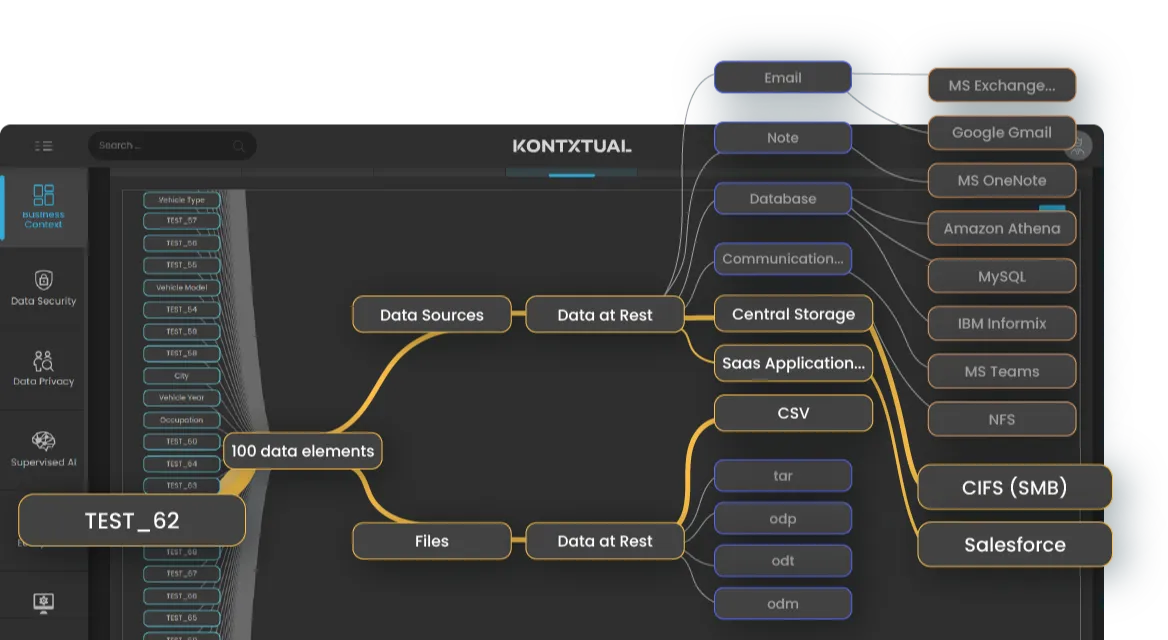
Continuously discover and classify sensitive data across cloud, SaaS, on-prem, and even mainframe.
Continuously discover and classify sensitive data across cloud, SaaS, on-prem, and even mainframe.
Third-party testing by The Tolly Group confirms Kontxtual’s industry-leading accuracy and throughput at enterprise scale:

Sensitive data sprawls across data lakes, SaaS, legacy file shares, and mainframes.
You need accurate visibility with context, and the ability to act—without adding manual burden.
KontxtualTM connects discovery to classification and enforcement in a continuous loop—so you always know what you have, how it’s used, and what to do next.
Step 1 - Discover
Continuously
Map structured and unstructured data across cloud, SaaS, on-prem, mainframe, and managed file transfer workflows to maintain a live inventory of sensitive data and risk-weighted views by system, owner, and purpose.
Step 2 — Classify Data in Full Context
Kontxtual creates a living, continuously updated record for every data element. By linking data to identity, flow, policy, and risk in a multidimensional graph, it shows where sensitive data lives, how it moves, and what controls apply.
Step 3 — Orchestrate the Next Right Step
Trigger access changes, masking, encryption, retention, and ticketing through the tools you already use—with audit-ready evidence generated automatically.
When discovery and classification run continuously, you don’t just find data, you stay ahead of risk. Here’s what that means in practice:
Global enterprises are turning fragmented visibility into real control with KontxtualTM. By pairing continuous discovery with contextual classification, they’re reducing risk, speeding compliance, and cutting manual effort.
KontxtualTM connects directly with your existing stack to operationalize compliance—no rip-and-replace.
Auto-generate and track remediation tickets
Stream alerts into SIEM workflows
Apply policies across structured data sources
Extend classification and labeling to Microsoft estates
Sync data classification and lineage with governance catalogs
KontxtualTM extends discovery and classification into continuous protection across your stack, so you can expand to other high-impact use cases.

Unify discovery, context, and response across environments.

Govern external data transfers without slowing down partner workflows.
Identify weak encryption and prepare for quantum-safe standards.