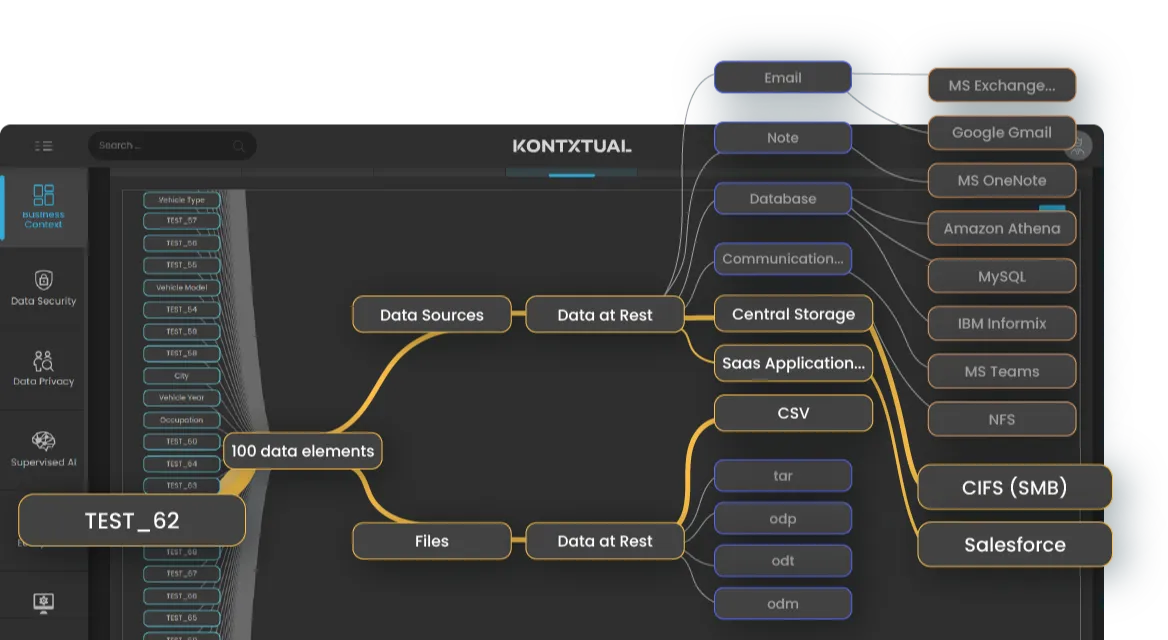
The problem isn’t just finding data. It’s trusting it, governing it, and taking meaningful action at scale. Most tools fall short because they:

Reduce Risk Exposure with dynamic least-privilege enforcement at the point of access.

Accelerate Compliance through automated controls mapped to GDPR, HIPAA, PCI, and sector frameworks.

Lower Operational Overhead by eliminating role explosion and manual entitlement reviews.

Support Digital Transformation with consistent governance across modern and legacy systems.

Ensure Verifiable Oversight with audit-ready logs aligned to business and regulatory requirements
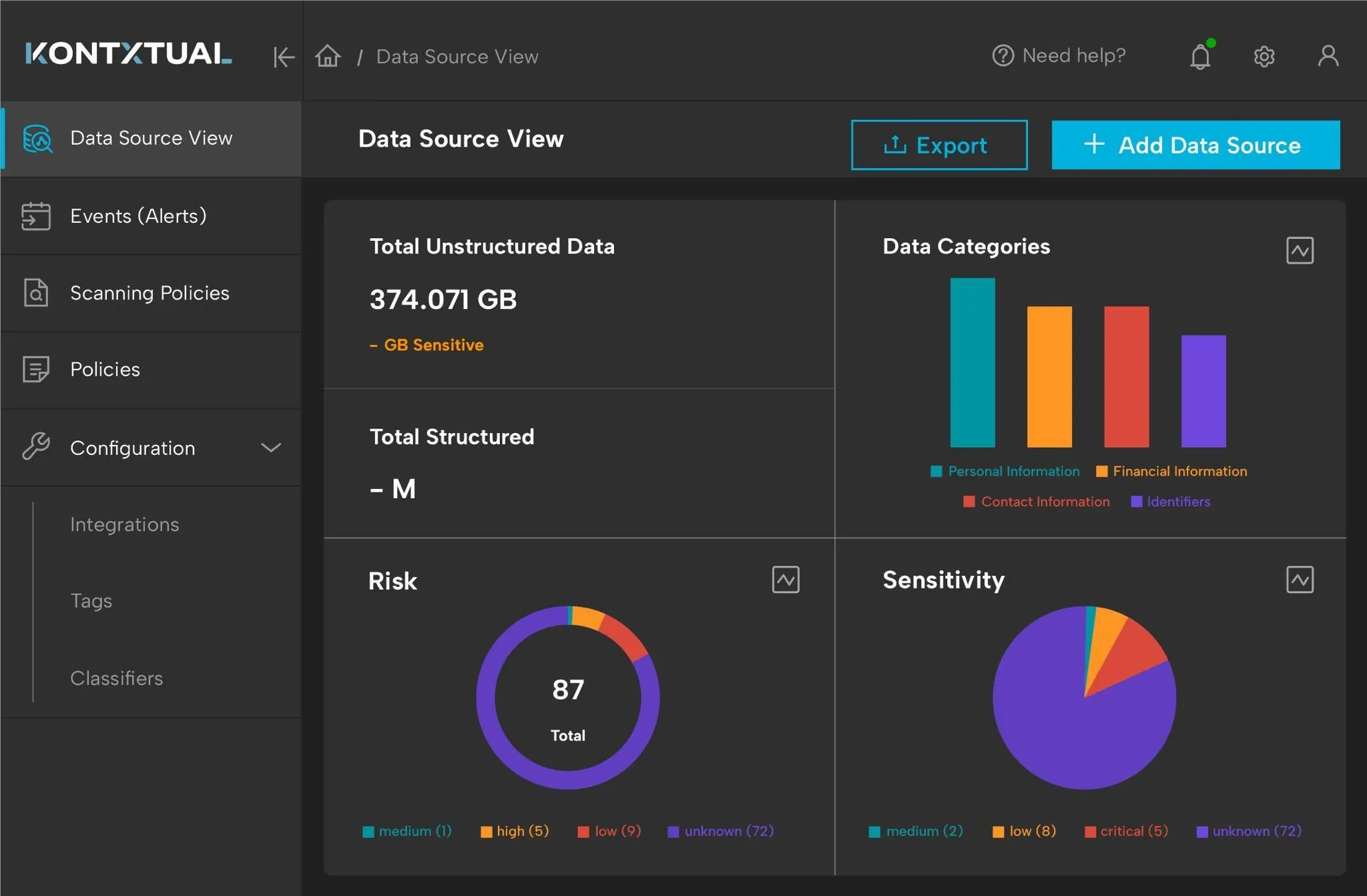
KontxtualTM was built to close these gaps and give organizations the contextual visibility, trust, and control they’ve been missing.













.svg)