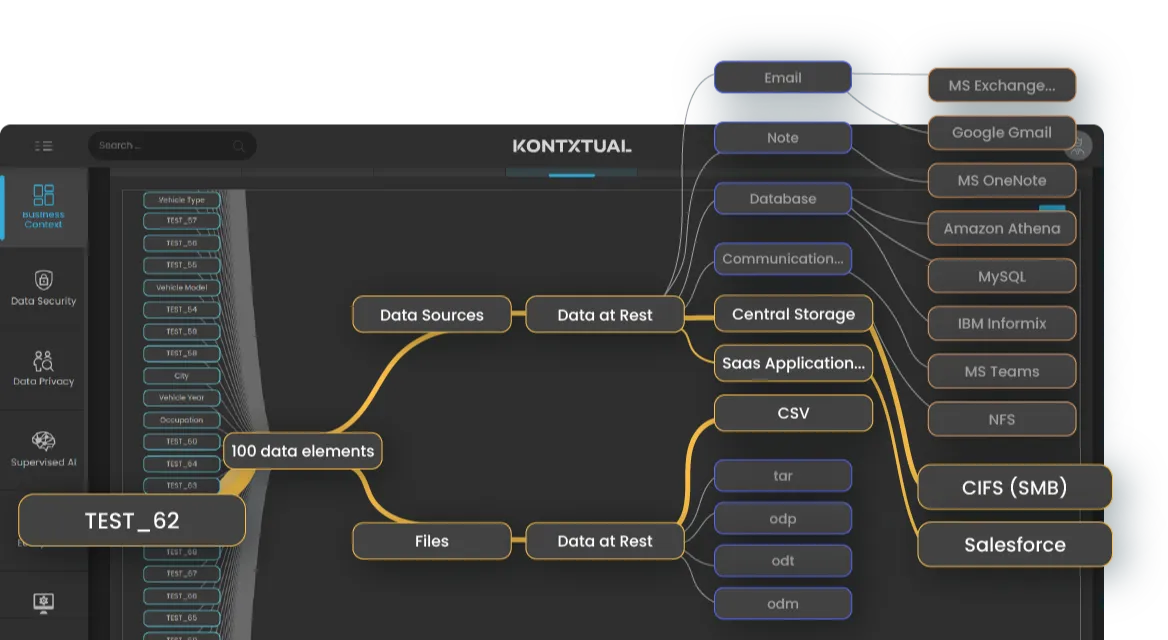
Multidimensional Data Mapping
Mainframe Security Posture Management (MSPM)
Continuously scans for sensitive data across structured, unstructured, cloud, on-prem, and legacy environments.
Applies AI- and context-driven labels based on data type, use, origin, and compliance obligations.
Connects data assets to users, systems, flows, and business context.
Maps and analyzes who has access to sensitive data, how, and why.
Calculates risk based on sensitivity, location, access, usage patterns, and compliance misalignment.
Automates downstream workflows like redaction, retention, access removal, or encryption based on policy triggers.
Discovers and classifies sensitive data before it enters AI training pipelines.
Extends discovery and classification to VSAM, Db2, IMS, and other mainframe systems.
Analyzes sensitive data usage across BI tools, data lakes, and analytic pipelines.
Maintain a real-time data inventory for automated enforcement and audit readiness.
Reduces manual effort and improves accuracy in identifying regulated and high-risk data.
Builds a live, actionable foundation for governance, risk scoring, and audit.
Reduce access risk, enforce least privilege, and uncover dormant accounts or overexposure.
Helps teams prioritize the most urgent exposures for remediation or protection.
Drives measurable enforcement without manual bottlenecks or swivel-chair workflows.
Prevent IP leakage and regulatory violations in GenAI, analytics, and ETL processes.
Bring legacy systems into compliance without agents or copybooks.
Ensure governed, trusted data fuels AI, analytics, and reporting.