Sensitive Data Intelligence: The Future of Cybersecurity
TL;DR – 1touch.io pioneered the groundbreaking category of tools known as “Sensitive Data Intelligence,” which have transformed the way sensitive data is discovered, classified, and inventoried. By adding business context and data insights to this inventory, organizations gain the ability to make well-informed decisions. This third-generation solution tackles the challenges faced by its predecessors, offering unparalleled efficiency and effectiveness.
From Tools to Intelligence: Revolutionizing Cybersecurity
The domain of cybersecurity has long relied on a multitude of tools, each serving a specific purpose. We have foundational tools, tools to enhance their effectiveness, and even tools that sit on top of the security stack to extract more insights. Frameworks, such as “Defense in depth,” “total security,” and “Zero Trust,” have been coined by consultants and analysts to describe the ideal set of tools and processes needed in order to establish robust security.
However, at the core of these frameworks lies an assumption that organizations have a deep understanding of their crown jewels—the sensitive data that requires protection.
Unfortunately, this assumption falters in reality due to the exponential growth of data within organizations, making it humanly impossible to keep track of all the crown jewels and the various places where this data may reside. This challenge becomes even more complex when business units and users perceive security as an obstacle that hinders their day-to-day operations. Organizations strive to secure their crown jewels and sensitive data, but they also want to empower users to perform their jobs without hindrance.
Balancing these conflicting needs led to the emergence of tools specializing in discovering, classifying, and inventorying sensitive data. In theory, this seemed like a simple solution that used regular expressions to identify patterns in data to underpin classification. However, in practice data discovery and classification has proven to be a long-standing challenge with negative connotations among users.
First and Second-Generation Tools: Challenges and Limitations
Let’s examine the different generations of sensitive data security tools and their evolution.
First Generation – Embedded Compliance-Based Tools
The first generation of discovery and classification solutions emerged over 15 years ago. These tools primarily focused on compliance requirements, with discovery and classification capabilities embedded within larger tools like Database Activity Monitoring (DAM), Data Access Governance (DAG), or Data-Loss Prevention (DLP). Their purpose was to demonstrate to auditors that proper controls – monitoring, policies, and blocking – were in place to protect sensitive data.
Limitations of Compliance-Based Tools for Data Protection
While most large organizations have adopted these tools, they often elicit frustration from users, due to their burdensome and limited classification capabilities and challenges in usability. First-generation classification capabilities typically rely on Regex patterns and scanning processes fail to extend beyond column headers or metadata, resulting in the loss of valuable information. False positives are common, calling into question their effectiveness in providing intelligence on the sensitive data location.
Finally, these compliance-based tools are often band-aid solutions that do not address the core problems of security, privacy, or governance. Forward thinking organizations strive for more…
Second Generation – Standalone Reactive Tools
In response to regulations like GDPR, the second generation of discovery and classification tools emerged in 2015 and 2016. Originally focused on privacy use cases, these tools expanded their scope to encompass security, governance, and data science applications. Many of them operate as standalone solutions, capable of scanning structured, unstructured, cloud and on-premises data. Their classification techniques expanded beyond Regex to include NLP (Natural Language Processing) functions and some light AI. This generation of market leaders have achieved substantial revenue, validating the demand for these capabilities.
Limitations of Reactive Data Discovery and Classification Tools
While second-generation tools have proven successful in reactive tasks, such as fulfilling DSAR (Data Subject Access Requests) or creating alerts for sensitive data movement outside approved areas, they face significant challenges in terms of scale and performance. Organizations require these tools to scan petabytes of data within reasonable timeframes, but many tools fail to meet this demand. Customers who initially adopted these tools are now facing subscription renewals and seeking alternatives due to the inability of incumbents to deploy and scale to meet their requirements.
These challenges have paved the way for the third generation of tools – Sensitive Data Intelligence.
The Emergence of Sensitive Data Intelligence
Recognizing the limitations of previous generations of tools, a new era of solutions has emerged.
Sensitive Data Intelligence Defined
Before we go any further, let’s define Sensitive Data Intelligence, a term first coined by 1touch.io to address the fundamental questions around sensitive data protection.

Sensitive data intelligence represents the next evolution of AI/ML-driven discovery and classification, complemented by layers of business context and data insights. It empowers organizations to make informed decisions at scale.
Third Generation Tools: Proactive Sensitive Data Intelligence
Sensitive Data Intelligence fully harnesses the power of AI/ML-driven discovery and classification to provide proactive data security, privacy, governance and compliance. Leveraging advanced algorithms and business context, it offers comprehensive insights into an organization’s sensitive data landscape at scale.
The Power of Proactive Sensitive Data Intelligence
Proactive intelligence, whether in the realm of threat intel, HUMINT, or SIGINT, involves transforming raw data inputs into cohesive output that inform decisions before an active threat requires a response. Proactivity leads to cost savings, reduced risk, and enhanced security posture—attributes critical for modern enterprises. In the context of discovery and classification, Sensitive Data Intelligence encompasses the ability to find and understand sensitive data—structured, unstructured, cloud, on-premises, and even mainframes—at scale.
Furthermore, it correlates these findings with other telemetry data to provide a comprehensive view of 1) where sensitive data resides; 2) what sensitive data is adequately protected; 3) what sensitive data requires additional safeguards; and 4) what non-sensitive data can forego security controls, freeing up valuable resources.
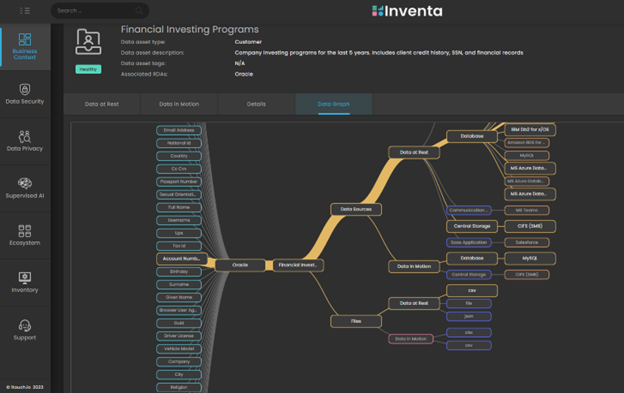
Third-generation tools, exemplified by 1touch.io Inventa, leverage AI/ML throughout the solution to quickly find sensitive data, assess existing security controls, and prioritize critical assets that require further protection. These tools operate continuously and autonomously, minimizing the need for human intervention. Machine learning algorithms continuously refine the system, rendering false positives and negatives nearly extinct, even at petabyte scale. 1touch.io, the pioneer in the Sensitive Data Intelligence space, coined the term to differentiate it from traditional discovery and classification approaches.
Benefits of Sensitive Data Intelligence
Here are a few examples of how Sensitive Data Intelligence transforms cybersecurity:
Business Context: How to Reconcile “John Doe”
One distinguishing characteristic of Sensitive Data Intelligence is its focus on business context. Simply knowing that a credit card number exists in an Oracle database is helpful, but not actionable or proactive. However, deriving insights that link the credit card number to an individual like John Doe, a German citizen and customer who recently purchased dog food, and discovering that the credit card number was found in a U.S data center, provides a clear call to action. Armed with this information, users can take appropriate measures, such as quarantining the data, removing it, and blocking data flow from Europe to the United States. This exemplifies the essence of Sensitive Data Intelligence.
Easy Consumption: Lessons from the Intelligence Community
Moreover, Sensitive Data Intelligence is designed to be accessible to a wide range of people and organizations. Similar to how the CIA shares intelligence with multiple agencies and military branches to ensure preparedness, Sensitive Data Intelligence takes a similar approach. The system is API-driven and offers an extensive API guide, enabling downstream control tools like encryption, DAM, SIEM (Security Information Event Management), SOAR (Security Orchestration, Automation and Response), DLP and others to leverage the intelligence it provides. By doing so, organizations can achieve greater ROI, as these tools can focus solely on the data that truly matters. For instance, Inventa seamlessly integrates with various SIEM solutions, reducing alerts by up to 85%, resulting in cost savings and faster incident response times.
Orchestration: Automating Proactive Responses
Finally, Sensitive Data Intelligence orchestrates security, privacy, governance and compliance actions automatically based on the needs of the organization. When thinking about security automation, often SOAR comes to mind, but those solutions orchestrate actions based on playbooks that are human defined. Sensitive Data Intelligence is capable of orchestrating actions based on the sensitive data being found and classified in the environment, fully leveraging the value and understanding of the crown jewels to inform security posture. For instance, Inventa can orchestrate a broad range of actions to change monitoring policies, DLP tags and blocking policies, SOAR playbooks, SIEM alerting, ticketing, and even encrypting individual files.
Embrace the Future of Cybersecurity with Sensitive Data Intelligence
Sensitive Data Intelligence represents a paradigm shift in data protection, empowering organizations to stay one step ahead of the ever-evolving threat landscape. By proactively discovering, classifying, and safeguarding sensitive data, organizations can ensure sustainable and automated protection, effectively addressing compliance requirements and minimizing the risk of data breaches.
Embrace the future of cybersecurity—explore the transformative potential of Sensitive Data Intelligence and secure your organization’s sensitive assets today. Demo 1touch.io Inventa’s sensitive data intelligence and see the value for yourself.
